
Research & Development
Rad Laboratories develops architecturally distinct cognitive infrastructure systems
Overview
A human-centered interface layer connecting advanced AI infrastructure with real-world reasoning.
Built on coordinated AI systems, photonic processing foundations, and bilateral cognitive architectures.
Structured Cognitive Infrastructure
Current AI systems operate as isolated capabilities. Rad Laboratories builds the connective architecture that transforms fragmented intelligence into coordinated, human-integrated reasoning systems.
Fragmentation
Problem
Coordination
Challenge
Real-World Reasoning
Gap
.
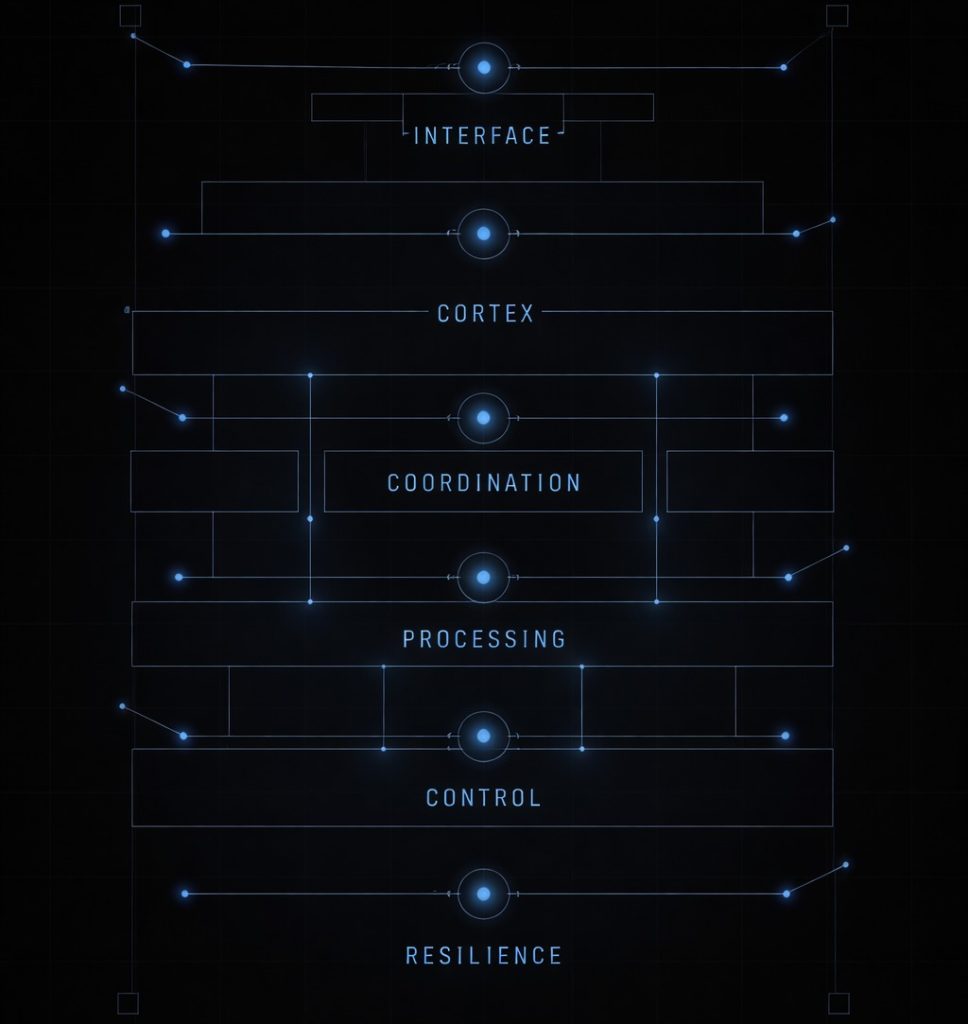
System Architecture Stack
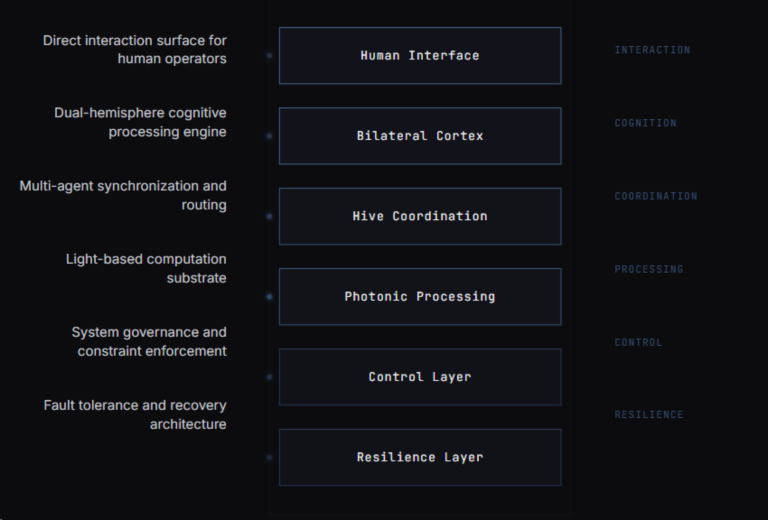
Core Architecture Overview
Luxherion Hive™
A distributed AI coordination architecture designed to operate across multiple computational environments.
The system integrates
Triangulated AI encoding
Distributed intelligence networks
Advanced verification and alignment layers
Hybrid classical / quantum-logic simulation models
Goal
To improve resilience, coherence, and verification across complex technological systems.
Security Analysis
Security Architecture Matrix
Structured comparison of defense architectures against escalating attack paradigms.
CLASSICAL ATTACK
QUANTUM ATTACK
POLYMORPHIC INTELLIGENCE ATTACK
OMNIPHORIC INTELLIGENCE ATTACK
CLASSICAL DEFENSE
Adequate against ordinary adversaries if well maintained. Relies on fixed algorithms, fixed trust anchors, and static perimeter assumptions.
Structurally vulnerable where public-key systems depend on RSA/ECC. Once the primitive fails, trust can collapse quickly.
Weak at boundaries. Adaptive attackers can exploit protocol translation, operator behavior, downgrade paths, and cross-layer gaps.
Highly vulnerable. A field-level attacker can identify the cheapest total-collapse path across math, systems, humans, governance, and recovery logic.
PQC DEFENCE
Stronger against future cryptanalytic shocks in public-key infrastructure. Better than classical defense for long-horizon survivability.
Designed specifically to resist known quantum attacks against key exchange and signatures. Major improvement if correctly implemented.
Better, but still often too algorithm-centric. Can resist the math while still leaking through implementation, orchestration, and trust transitions
Improved resilience, but not sufficient by itself. Omnimorphic attackers do not need to defeat only the PQC primitive; they can target system architecture, lifecycle handling, identity recovery, and trust delegation.
POLYMORHIC DEFENCE
Strong against static attackers because the system changes form by context. Reduces value of fixed attack playbooks.
Better than plain PQC if the architecture can shift forms and rotate protection modes under stress. Still may be vulnerable if adaptation rules are predictable.
Stronger, because the system can alter posture based on conditions. However, it may still be defeated if the attacker learns the adaptation logic.
Moderately resilient, but at risk if attackers model the transformation rules themselves. If attackers can predict “how the system changes,” polymorphism becomes legible rather than protective.
OMNIMORHIC DEFENCE
Extremely strong if well governed. Security is no longer resting on one primitive or one mode of validation.
Potentially the best long-term posture, because quantum breaking of one layer does not equal total failure if architecture is distributed and validated across layers.
Very strong if forms are constitutionally separated. Adaptive attackers may penetrate one domain without obtaining full system control.
This is the true endgame context. Omnimorphic defense can survive only if secrecy, identity, execution, routing, recovery, audit, and trust renewal are separated and cross-validated. Otherwise complexity becomes weakness.
CLASSICAL DEFENSE
CLASSICAL ATTACK
Adequate against ordinary adversaries if well maintained. Relies on fixed algorithms, fixed trust anchors, and static perimeter assumptions.
QUANTUM ATTACK
Structurally vulnerable where public-key systems depend on RSA/ECC. Once the primitive fails, trust can collapse quickly.
POLYMORPHIC INTELLIGENCE ATTACK
Weak at boundaries. Adaptive attackers can exploit protocol translation, operator behavior, downgrade paths, and cross-layer gaps.
OMNIPHORIC INTELLIGENCE ATTACK
Highly vulnerable. A field-level attacker can identify the cheapest total-collapse path across math, systems, humans, governance, and recovery logic.
PQC DEFENCE
CLASSICAL ATTACK
Stronger against future cryptanalytic shocks in public-key infrastructure. Better than classical defense for long-horizon survivability.
QUANTUM ATTACK
Designed specifically to resist known quantum attacks against key exchange and signatures. Major improvement if correctly implemented.
POLYMORPHIC INTELLIGENCE ATTACK
Better, but still often too algorithm-centric. Can resist the math while still leaking through implementation, orchestration, and trust transitions
OMNIPHORIC INTELLIGENCE ATTACK
Improved resilience, but not sufficient by itself. Omnimorphic attackers do not need to defeat only the PQC primitive; they can target system architecture, lifecycle handling, identity recovery, and trust delegation.
POLYMORHIC DEFENCE
CLASSICAL ATTACK
Strong against static attackers because the system changes form by context. Reduces value of fixed attack playbooks.
QUANTUM ATTACK
Better than plain PQC if the architecture can shift forms and rotate protection modes under stress. Still may be vulnerable if adaptation rules are predictable.
POLYMORPHIC INTELLIGENCE ATTACK
Stronger, because the system can alter posture based on conditions. However, it may still be defeated if the attacker learns the adaptation logic.
OMNIPHORIC INTELLIGENCE ATTACK
Moderately resilient, but at risk if attackers model the transformation rules themselves. If attackers can predict “how the system changes,” polymorphism becomes legible rather than protective.
OMNIMORHIC DEFENCE
CLASSICAL ATTACK
Extremely strong if well governed. Security is no longer resting on one primitive or one mode of validation.
QUANTUM ATTACK
Potentially the best long-term posture, because quantum breaking of one layer does not equal total failure if architecture is distributed and validated across layers.
POLYMORPHIC INTELLIGENCE ATTACK
Very strong if forms are constitutionally separated. Adaptive attackers may penetrate one domain without obtaining full system control.
OMNIPHORIC INTELLIGENCE ATTACK
This is the true endgame context. Omnimorphic defense can survive only if secrecy, identity, execution, routing, recovery, audit, and trust renewal are separated and cross-validated. Otherwise complexity becomes weakness.
Differentiation
What Makes This Different
Traditional Systems
Data scale
Compute scale
Model size
Rad Laboratories
Multi-perspective reasoning
Coordinated intelligence
Application Domains
Real World Focus
AI Coordination systems
Distributed architectures designed to coordinate complex machine intelligence networks.
Human-AI Interface Environments
The RAD Apparatus platform explores ergonomic and cognitive environments for human interaction with advanced AI systems.
Systems designed to improve trust, integrity, and transparency across financial, communications, and governance infrastructures.
Guardian frameworks such as Quantum Mom explore human-centered alignment approaches for advanced AI.
Record
Rad Laboratories governs its master portfolio through a triangulated three-sleeve architecture aligned to commercial, sovereign, and strategic domains.
Development & Research Record
Rad Laboratories has conducted multi-year research and engineering development across multiple system domains.
144+
structured provisional patent filings completed to date
8M+
lines of architecture and simulation code completed
2,500+
system simulations and Monte Carlo tests completed
37
curated safety and guardian datasets compiled
4.2 TB
synthetic system development archive completed
As technological systems become more complex, the challenge facing civilization is no longer simply building new machines, but managing complexity, coherence, and system integrity at scale.
Status
Cognitive Architecture Testbed
Active development environment for validating architectural hypotheses and testing coordinated intelligence systems under controlled conditions.
• Active — Vancouver, BC Canada
Direction
Not incremental improvement.
Architecturally distinct cognitive infrastructure
Structured Reasoning
Coordinated Systems
Human Integration
Principles
Rad Laboratories focuses on long-horizon system development
Structural discipline
Controlled communication
Architecture-first design
Current Research Directions
Distributed AI coordination architectures
Infrastructure resilience systems
Hybrid quantum-logic simulation frameworks
Human-AI interaction environments
Ethical alignment models for advanced AI
Detailed technical materials are available through structured engagement.

Rad Laboratories
Private Research & Development
SECURE CONTACT
© 2026 Rad Laboratories. All rights reserved.